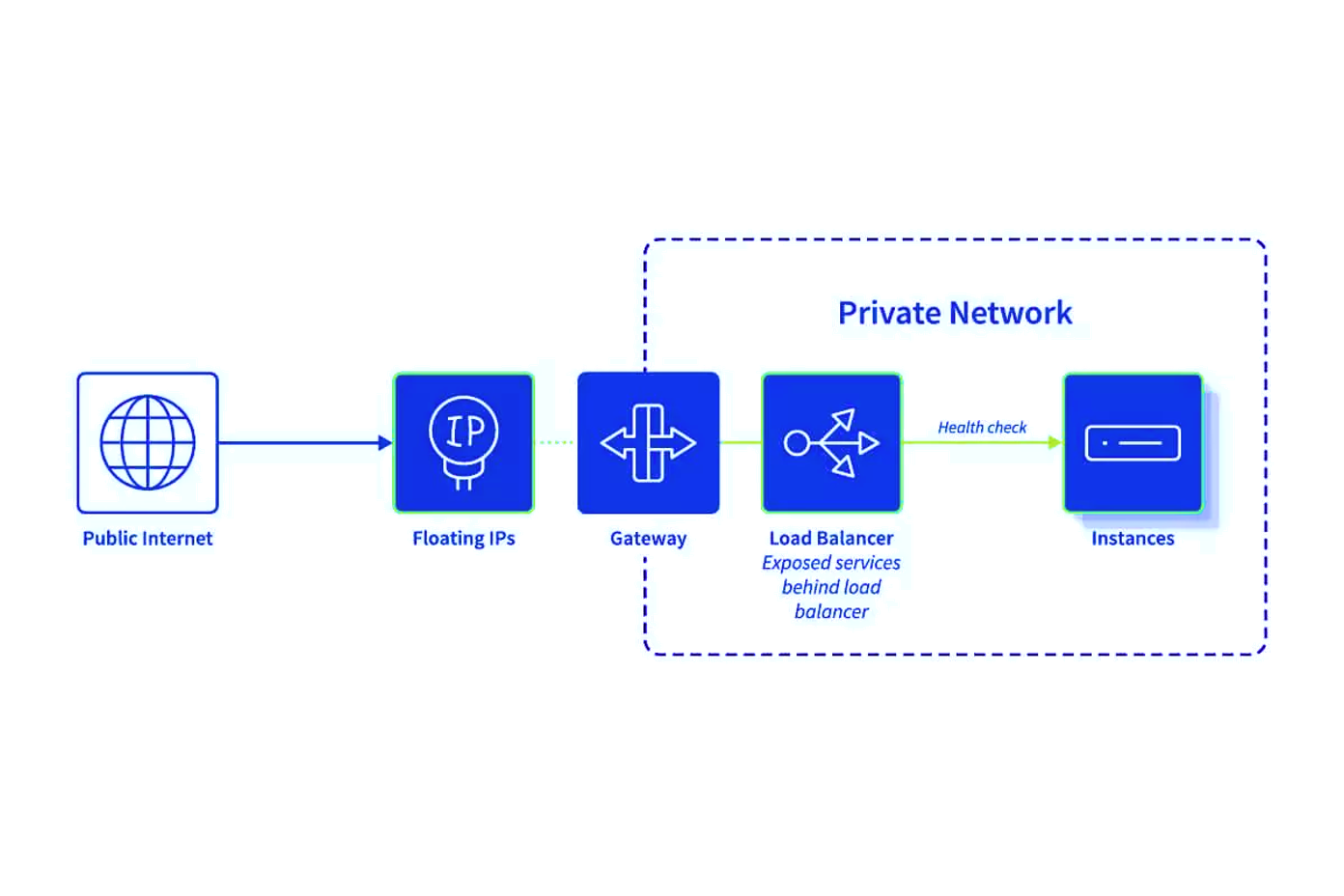
Load Balancer Scenario
In your design, Floating IP, Gateway, and Load Balancer collaborate harmoniously to establish the necessary network accessibility rules, ensuring the security levels you demand.
Access the Load Balancer via the Floating IP, which efficiently allocates incoming traffic to multiple instances. The instances behind the Load Balancer lack public IPs, preserving complete privacy and preventing direct external access. Enhance security with SSL encryption, and seamlessly update the Load Balancer transparently, thanks to the Floating IP being hosted at the Gateway level.